You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
Copy file name to clipboardExpand all lines: content/docs/data-access/definitions/access-policies.md
+17-17Lines changed: 17 additions & 17 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -23,7 +23,7 @@ In addition, two special types of access policies are available:
23
23
24
24
Access policies provide central, fine-grained control over sensitive data access. They can evaluate purpose, identity, authorization, location, , and more. They can range from simple "always allow resolution" policies to complex evaluations.
25
25
26
-

26
+

27
27
28
28
## Example Use Cases
29
29
@@ -58,7 +58,7 @@ Access Policies are composed from Access Policy Templates. Templates are paramet
58
58
59
59
### Template function
60
60
61
-
```
61
+
```javascript
62
62
functiongetAge(DOB) {
63
63
consttoday=newDate();
64
64
constbirthDate=newDate(DOB);
@@ -77,7 +77,7 @@ function policy(context, params) {
77
77
78
78
### Parameters to instantiate a policy
79
79
80
-
```
80
+
```javascript
81
81
// Example Policy Parameters (not specified in the template function)
@@ -88,7 +88,7 @@ Here is an example of how you can create a policy to check if the country claim
88
88
89
89
### Template function
90
90
91
-
```
91
+
```javascript
92
92
functionpolicy(context, params) {
93
93
constcountry=context.server.claims.country;
94
94
constspecifiedCountry=params.specified_country;
@@ -98,7 +98,7 @@ function policy(context, params) {
98
98
99
99
### Parameters to instantiate a policy
100
100
101
-
```
101
+
```javascript
102
102
// Example Policy Parameters (not specified in the template function)
103
103
constparams= { specified_country:"USA" };
104
104
```
@@ -109,7 +109,7 @@ If the country information is not in the JWT but in the client context, the poli
109
109
110
110
### Template function
111
111
112
-
```
112
+
```javascript
113
113
functionpolicy(context, params) {
114
114
constcountry=context.client.country;
115
115
constspecifiedCountry=params.specified_country;
@@ -119,7 +119,7 @@ function policy(context, params) {
119
119
120
120
### Parameters to instantiate a policy
121
121
122
-
```
122
+
```javascript
123
123
// Example Policy Parameters (not specified in the template function)
124
124
constparams= { specified_country:"USA" };
125
125
```
@@ -136,11 +136,11 @@ We provide a number of built-in functions available as global variables in your
136
136
137
137
The built-in `networkRequest` function allows you to reach external services via HTTPS requests. You can pass headers in the network request, allowing you to authorize into third-party services, such as Zendesk via Basic Auth. This feature is useful for scenarios where your policy needs to check external data, e.g. for verifying if an employee has been assigned an open ticket for the user whose data they are trying to access.
138
138
139
-
### Example:
139
+
### Example
140
140
141
141
This example shows how to make a network request to verify the user's country based on their IP address. Note that the interface for `networkRequest` is synchronous, as in the example below:
@@ -151,13 +151,13 @@ function policy(context, params) {
151
151
}
152
152
```
153
153
154
-
### Example:
154
+
### Example
155
155
156
-
This example shows how to verify an employee is active in a private employee directory, using Basic Auth.
156
+
This example shows how to verify an employee is active in a private employee directory, using Basic Auth.
157
157
158
-
#### Template Function:
158
+
#### Template Function
159
159
160
-
```
160
+
```javascript
161
161
functionpolicy(context, params) {
162
162
let isActiveEmployee =false;
163
163
@@ -181,7 +181,7 @@ function policy(context, params) {
181
181
182
182
#### Parameters to instantiate a policy
183
183
184
-
```
184
+
```javascript
185
185
// Example Policy Parameters (not specified in the template function)
186
186
constparams= {}; // No specific parameters needed for this example
187
187
```
@@ -192,11 +192,11 @@ const params = {}; // No specific parameters needed for this example
192
192
193
193
The `checkAttribute` function runs a permission check against the UserClouds authorization graph. If you are using UserClouds for authorization as a service, this can verify if a user has the necessary permissions. In short, it asks whether a given object (usually a user) has an attribute (e.g. "can-read" or "is-admin") on another object (which could be just about any entity in your system). You can read more about this in the [Authorization Documentation](https://docs.userclouds.com/reference/get_authz-checkattribute).
194
194
195
-
### Example:
195
+
### Example
196
196
197
197
**Use Case: Does the calling user have view permission on the target user?**
198
198
199
-
```
199
+
```javascript
200
200
functionpolicy(context) {
201
201
constcallingUserId=context.user.id;
202
202
consttargetUserId=context.params.targetUserId;
@@ -217,7 +217,7 @@ function policy(context) {
217
217
-`country_name`: the ISO 3166 country name, as defined [here](https://github.com/OpenStars/phonenumber/blob/8ad15782bef1/iso3166.go) ; and
218
218
-`country_code`: the numeric telephone country code
Copy file name to clipboardExpand all lines: content/docs/data-access/how-to-guides/create-an-access-policy.md
+2-4Lines changed: 2 additions & 4 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
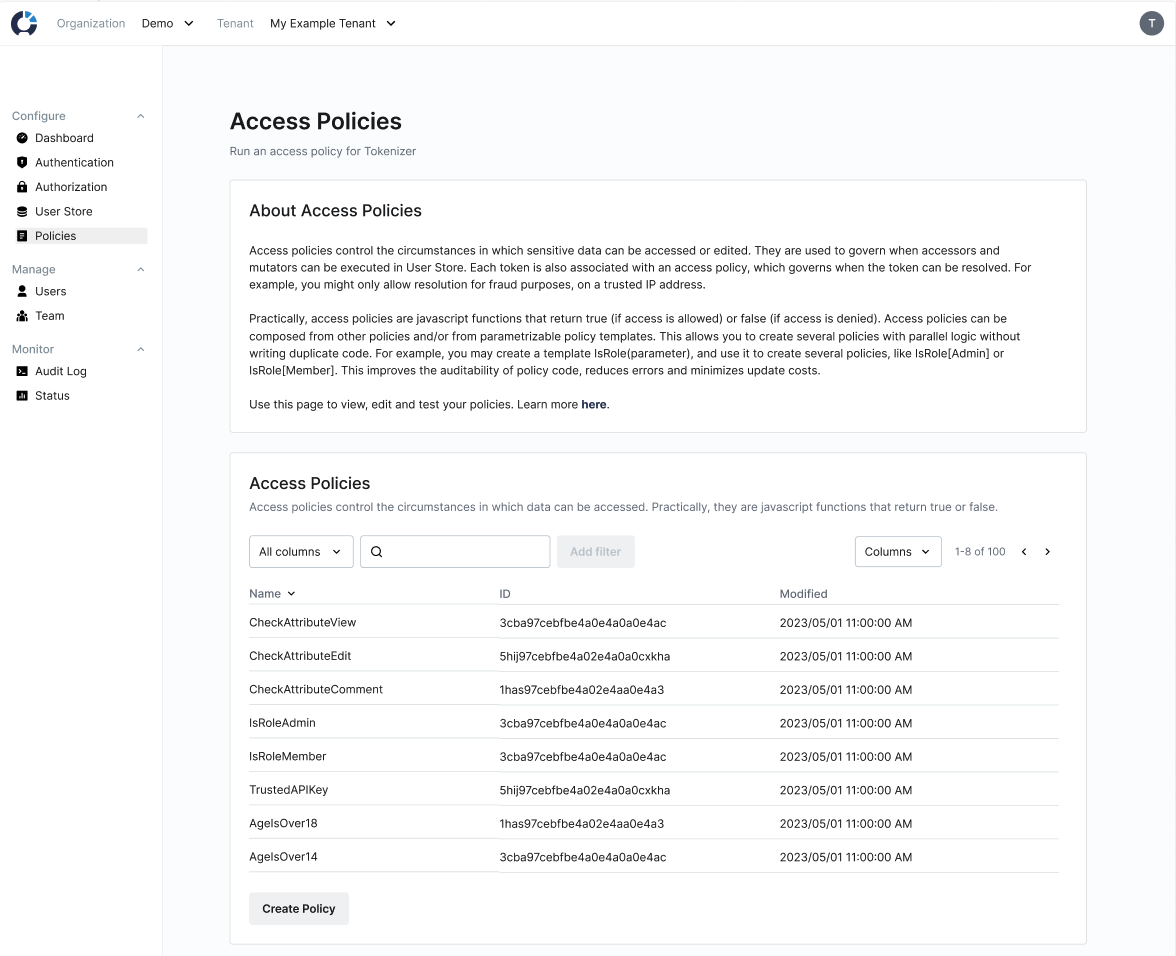
@@ -18,7 +18,6 @@ Access policies and templates are managed under the Access Rules element in the
18
18
19
19
20
20
21
-
22
21
## Creating Policy Templates in the UI
23
22
24
23
Policy templates are parametrizable functions that can be parametrized to create access policies. To create a policy template, go to the Policies page and click Create Policy Template.
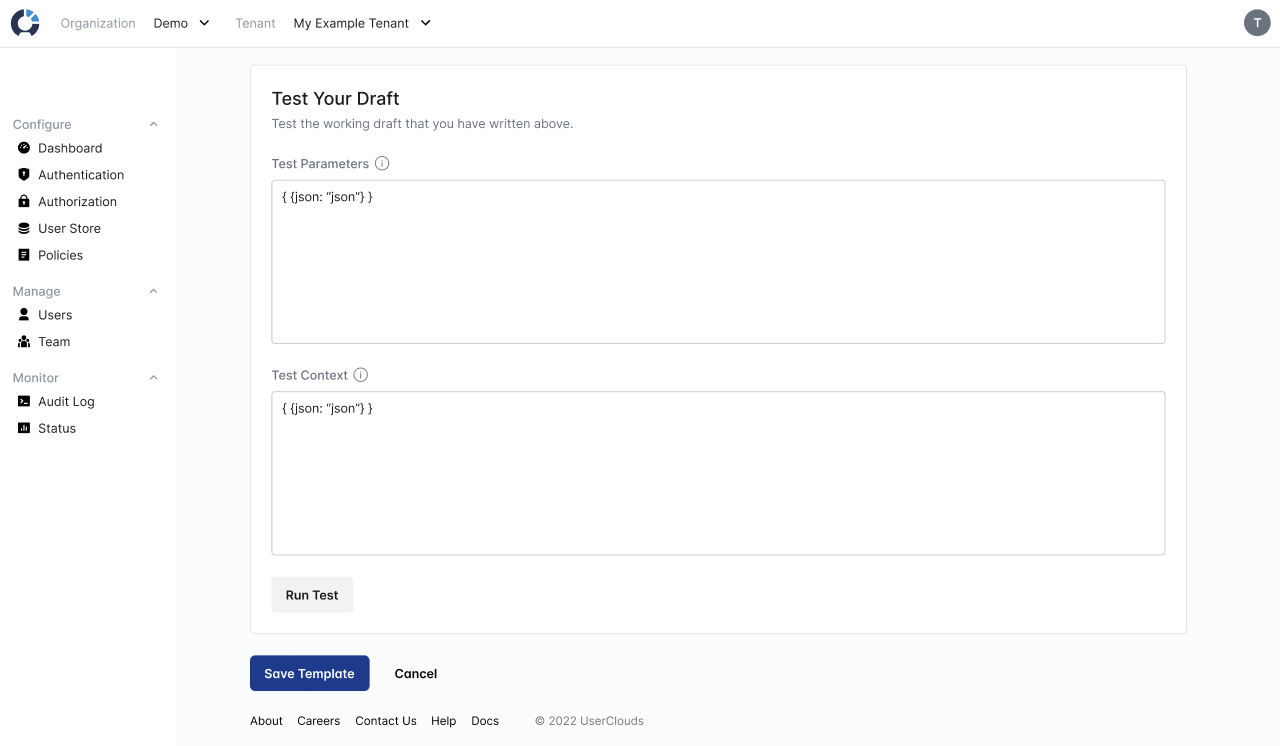
@@ -36,7 +35,6 @@ Use the "Test Your Draft" card at the bottom of the page to test your policy tem
36
35
37
36
38
37
39
-
40
38
## Creating Access Policies in the UI
41
39
42
40
**1 Open the Create Access Policy Page**
@@ -83,7 +81,7 @@ The checkAttribute function runs a permission check against the UserClouds autho
83
81
84
82
**Use Case: Does the calling user have view permission on the target user?**
85
83
86
-
```
84
+
```javascript
87
85
functionpolicy(context) {
88
86
constcallingUserId=context.user.id;
89
87
consttargetUserId=context.params.targetUserId;
@@ -103,7 +101,7 @@ Parametrizable templates let you create flexible policies by adjusting parameter
Once you have configured a <<glossary:mutator>>, you are ready to edit the user data and consents in your store. This can be done by executing the mutator.
9
+
Once you have configured a <<glossary:mutator>>, you are ready to edit the user data and consents in your store. This can be done by executing the mutator.
10
10
11
11
## How to execute a mutator
12
12
13
-
There are two ways to execute a mutator:
13
+
There are two ways to execute a mutator:
14
14
15
15
- Download and deploy your tenant's code-generated UserClouds SDK, and call the mutator indirectly using its SDK function name
16
-
- Call the [ExecuteMutator API](https://docs.userclouds.com/reference/post_userstore-api-mutators)
16
+
- Call the [ExecuteMutator API](https://docs.userclouds.com/reference/post_userstore-api-mutators)
17
17
18
18
When calling the ExecuteMutator API directly you pass:
19
19
@@ -34,7 +34,7 @@ When you execute a mutator, the following steps happen in sequence:
34
34
35
35
1. The mutator validates and normalizes the inbound data for each column associated with the mutator, using the configured <<glossary:data normalizer>> for that column.
36
36
2. The mutator finds candidate user records to update based on the mutator <<glossary:selector>> clause and the passed in <<glossary:SelectorValues>>.
37
-
3. Two access policies are applied to each selected user record: the global baseline policy for mutators (learn more [here](https://docs.userclouds.com/docs/apply-global-protection-policies)) and the mutator's own <<glossary:access policy>> composition. This step may involve evaluating the provided client context or any user-specific data already present in the User Store to determine if the write operation is permitted for each selector user record.
37
+
3. Two access policies are applied to each selected user record: the global baseline policy for mutators (learn more [here](https://docs.userclouds.com/docs/apply-global-protection-policies)) and the mutator's own <<glossary:access policy>> composition. This step may involve evaluating the provided client context or any user-specific data already present in the User Store to determine if the write operation is permitted for each selector user record.
38
38
4. If the access policy passes for the user, the mutator reconciles the normalized changes for each mutator column against existing user data, utilizing full mutation or partial mutation rules according to the column's configuration (see below for more detail).
39
39
5. Any resulting changes to the user's data and associated consents are saved to the store.
40
40
@@ -65,7 +65,7 @@ For this example, assume we are updating a column configured to be an array of s
65
65
66
66
1.**insert value with operational and marketing consents**
67
67
68
-
```
68
+
```plaintext
69
69
ValueAndPurposes = {
70
70
Value: [“foo”, “bar”],
71
71
PurposeAdditions: [“operational”, “marketing”],
@@ -76,6 +76,7 @@ For this example, assume we are updating a column configured to be an array of s
76
76
("bar", ["operational", "marketing"]),
77
77
]
78
78
```
79
+
79
80
2.**add data_science and remove marketing consents for existing values**
80
81
81
82
```
@@ -90,6 +91,7 @@ For this example, assume we are updating a column configured to be an array of s
Copy file name to clipboardExpand all lines: content/docs/data-access/how-to-guides/enforce-rate-limiting.md
+7-7Lines changed: 7 additions & 7 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -20,7 +20,7 @@ UserClouds applies rate limits to a given user based on the `sub` (subject) clai
20
20
21
21
The `AccessPolicyThresholds` structure defines the parameters for rate limiting:
22
22
23
-
```
23
+
```javascript
24
24
type AccessPolicyThresholds = {
25
25
announce_max_execution_failure: boolean;
26
26
announce_max_result_failure: boolean;
@@ -39,7 +39,7 @@ Execution limits control how often an action can be performed within a specific
39
39
40
40
Execution limits execute specially when a paginated accessor is called. The initial call is treated as one execution. Paging forward or backward from that initial call is not counted as another execution.
41
41
42
-
### Behavior:
42
+
### Behavior
43
43
44
44
- If `announce_max_execution_failure` is true, a 429 (Too Many Requests) error is returned when the limit is exceeded for accessors and mutators. Failures for token resolution are always silent (i.e., the token is not resolved).
45
45
- If `announce_max_execution_failure` is false, the request does not fail, but no actions will occur. That is, no results are returned (for accessors), modifications are not applied (for mutators), or tokens are not resolved (for token resolution).
@@ -50,13 +50,13 @@ Result limits control the number of results that can be returned or affected by
50
50
51
51
-`max_results_per_execution`: Maximum number of results affected by a single execution. If this is 0, the limit is turned off.
52
52
53
-
### Limit definition:
53
+
### Limit definition
54
54
55
55
- For accessors, this limit applies to the total number of results that could be returned, across all pages (if paginated). For example, an accessor that could return 6 different pages of 100 records each would exceed a 500 result limit, even though each individual page size is within the limit.
56
56
- For mutators, it applies to the number of records modified.
57
57
- For token resolution, it applies to the number of tokens resolved.
58
58
59
-
### Behavior:
59
+
### Behavior
60
60
61
61
- If `announce_max_result_failure` is true, a 400 (Bad Request) error is returned when the limit is exceeded.
62
62
- If `announce_max_result_failure` is false, the request does not fail, but no actions will occur. That is, no results are returned (for accessors), no modifications are applied (for mutators), or no tokens are resolved (for token resolution).
@@ -65,15 +65,15 @@ Result limits control the number of results that can be returned or affected by
65
65
66
66
Rate limiting is enabled by associating an access policy with rate limits to a mutator, accessor, or token. For tokens, the access policy is specified at token creation time (e.g. via the token resolution policy on an accessor returning the token).
67
67
68
-
### Token Resolution Note:
68
+
### Token Resolution Note
69
69
70
70
Failures are always silent (no error code is returned), as token resolution requests may involve multiple access policies, some of which may have rate limits and some may not.
71
71
72
72
## Example Usage
73
73
74
74
To set rate limits for an access policy, configure the `AccessPolicyThresholds`:
The rate limit thresholds for an access policy may be changed after the access policy is created.
89
+
The rate limit thresholds for an access policy may be changed after the access policy is created.
90
90
91
91
Note that we only consider the thresholds for the top level access policy for the accessor / mutator / token resolution. Since an access policy can be composed of multiple access policies, a sub-policy may have usage thresholds. Those thresholds would be ignored.
Copy file name to clipboardExpand all lines: content/docs/data-access/proxy-and-plug-in-implementation/3-applying-access-policies-to-queries.md
+6-6Lines changed: 6 additions & 6 deletions
Display the source diff
Display the rich diff
Original file line number
Diff line number
Diff line change
@@ -14,16 +14,16 @@ Once you have re-pointed your application’s database queries, object store req
14
14
15
15
Access policies are evaluated per row of returned data from the database. Therefore, if an access policy evaluates row-specific data returned from the database (such as a target user’s date of birth), it may return a subset of records.
16
16
17
-
### To Apply an Access Policy to a Particular Query:
17
+
### To Apply an Access Policy to a Particular Query
18
18
19
19
1.**Trigger the Query, Request, or API Call**: Trigger the action in the application if you haven’t already (e.g., by loading a table of data, requesting an object from storage, or calling an API endpoint).
20
-
2.**Select and Edit the Query, Blob Store, or API Call:**
20
+
2.**Select and Edit the Query, Blob Store, or API Call:**
21
21
1.**For SQL Proxies:** In the UserClouds Console, go to Accessors (under Access Methods), find the relevant query in your list of data accessors, and click "Edit".
22
22
2.**For NoSQL Proxies:** In the UserClouds Console, navigate to Object Stores under User Data Storage in the side navigation, select the object store, and click "Edit".
23
23
3.**For API Proxies:** In the UserClouds Console, navigate to API connections under User Data Storage in the side navigation, select the API connection, and click "Edit".
24
24
3.**Add Access Policies**: Scroll down to the access policy section and add one or more access policies.
25
-
1.**For SQL Proxies:**Apply policies at the query level.
26
-
2.**For NoSQL Proxies:**Apply policies at the object store level, but you can also consider the file path as context (e.g., a user ID in the file path) for finer-grained access control.
25
+
1.**For SQL Proxies:**Apply policies at the query level.
26
+
2.**For NoSQL Proxies:**Apply policies at the object store level, but you can also consider the file path as context (e.g., a user ID in the file path) for finer-grained access control.
27
27
3.**For API Proxies**: Apply policies at the individual endpoint level.
28
28
4.**Define Policy Logic**: If adding two or more access policies, define whether all policies or one policy must be true for the overall policy to pass, by ANDing or ORing the policies together.
29
29
5.**Save**: Click "Save".
@@ -38,7 +38,7 @@ Access policies can evaluate context passed in the request. Context can be inclu
38
38
39
39
This example shows how context is added to a query using comments:
40
40
41
-
```
41
+
```sql
42
42
SELECT name, email, phone FROM users WHERE id =1234/*geo=’uk’ user=’albus-dumbledore’*/
43
43
```
44
44
@@ -48,7 +48,7 @@ SELECT name, email, phone FROM users WHERE id = 1234 /*geo=’uk’ user=’albu
48
48
49
49
This example shows how an access policy might use the context to enforce access control:
50
50
51
-
```
51
+
```javascript
52
52
functionpolicy(context, params) {
53
53
// Allow access only if the calling user's geo is 'uk'
0 commit comments